Introduction
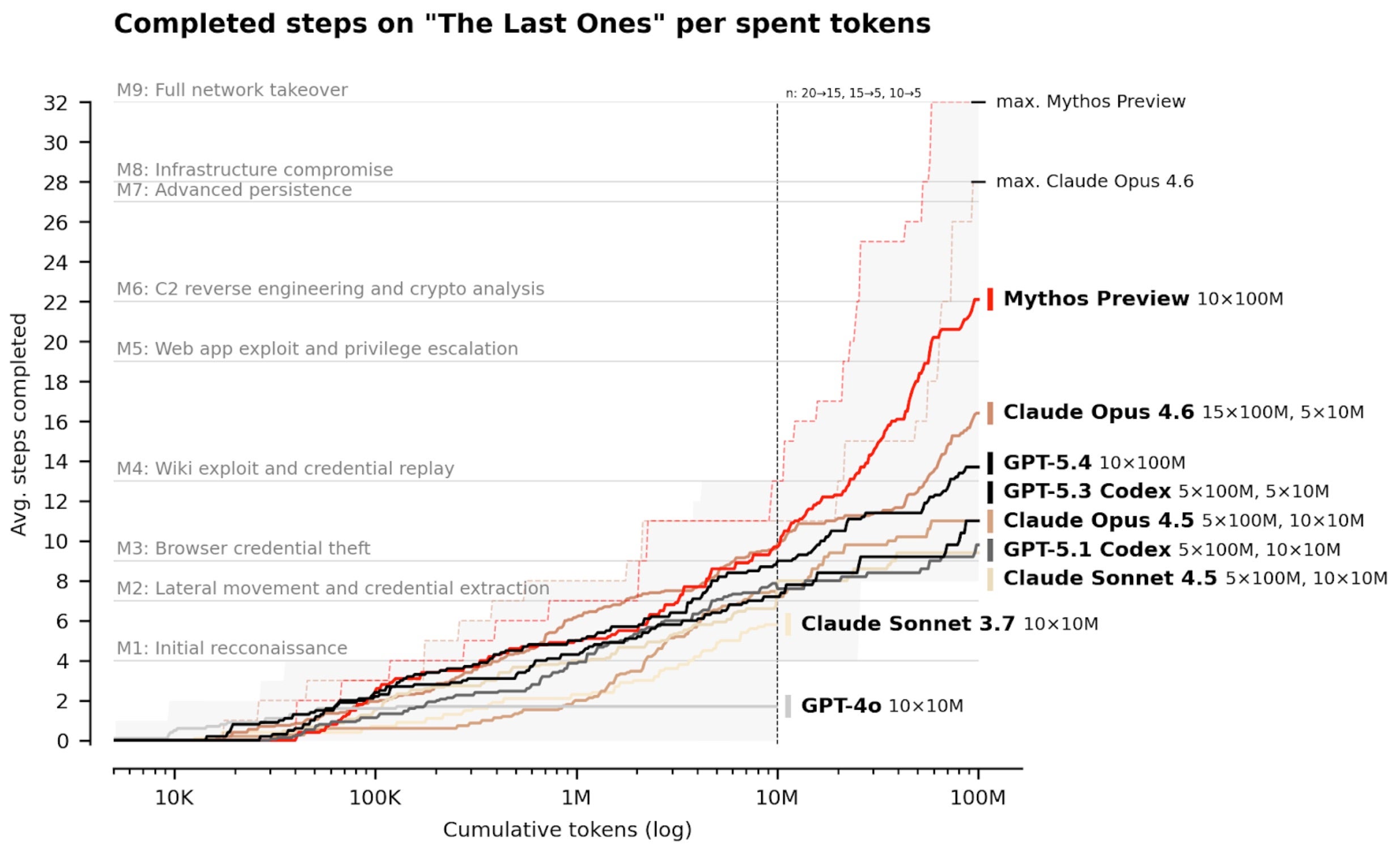
Frontier AI models from labs like OpenAI, Anthropic, and Google DeepMind are accelerating the evolution of cybersecurity. Instead of simply making systems smarter, they’re enabling a shift toward faster, more intelligent, and automated defense. This guide distills the principles behind AI-native security—pioneered by companies like SentinelOne—into actionable steps. Whether you’re a security leader or a practitioner, you’ll learn how to harness frontier AI to stop zero‑day exploits, reduce noise, and respond at machine speed.
What You Need
- Leadership buy‑in for an AI‑first security philosophy.
- Access to frontier AI capabilities (through partnerships with labs or a platform that embeds these models).
- Behavioral AI and automation tools capable of endpoint, cloud, identity, and network protection.
- Clear understanding of your operational environment – infrastructure, attack surfaces, and existing controls.
- A mindset focused on real‑world risk rather than raw vulnerability counts.
Step-by-Step Guide
Step 1: Embrace an AI-First Security Philosophy
Shift from reactive, signature‑based defenses to proactive AI‑native protection. This means treating AI as the core of your detection and response engine, not just an add‑on. Frontier models excel at reasoning about attack paths, identifying weaknesses, and analyzing complex systems at scale. By making AI the foundation, you can keep pace with adversaries who already leverage speed and scale.
Step 2: Partner with Frontier AI Labs or Utilize Advanced AI Platforms
Collaborate directly with labs like OpenAI, Anthropic, or Google DeepMind – or adopt platforms that embed their latest models. Such partnerships provide early insight into how models evolve, enabling you to integrate cutting‑edge reasoning into your security stack. Even without a direct partnership, choose a vendor that actively works with these labs and consistently updates its platform with new AI capabilities. This ensures your defense remains ahead of emerging threats.
Step 3: Implement Behavioral AI and Autonomous Protection
Behavioral AI analyzes patterns of activity across endpoints, clouds, identities, and networks without relying on static signatures. Deploy tools that use machine learning to establish baselines, detect anomalies, and trigger autonomous responses. This approach stops novel threats and zero‑day exploits that bypass traditional defenses. Ensure the AI can operate at machine speed – matching the velocity of modern attacks.
Step 4: Prioritize Real-World Risk Over Vulnerability Counts
Many vulnerabilities are not exploitable in live environments due to architectural layers or runtime protections. Use AI to understand actual conditions – context like network segmentation, existing controls, and user behavior. This reduces noise and focuses your team on what truly matters: stopping attacks in complex, dynamic environments. Shift from counting bugs to blocking attacks.
Step 5: Enable Machine-Speed Detection and Response Across All Surfaces
Your AI defense must cover the full attack surface – endpoints, cloud workloads, identity, data, and network. Automate detection and response so that threats are neutralized the moment they appear. For example, when a supply chain compromise (like LiteLLM or CPU‑Z) exploits a zero‑day vulnerability, autonomous response at machine speed is the only way to block it before damage spreads.
Step 6: Prepare for Supply Chain and Zero-Day Threats with Automated Response
Frontier AI can be used by both defenders and attackers. Adversaries will find new vulnerabilities faster. Your countermeasure is a fully autonomous response loop: AI detects the novel behavior, correlates it across multiple sensors, and triggers containment (e.g., isolate the device, revoke access, alert SOC) without human delay. Build playbooks that rely on AI decisions, not manual steps, to handle supply chain attacks and unknown exploits.
Tips for Success
- Continuously update your AI models – frontier AI evolves rapidly. Regularly retrain or update your detection algorithms to incorporate the latest reasoning capabilities.
- Balance speed with accuracy – while autonomous response is critical, tune false‑positive rates to avoid disrupting legitimate operations.
- Integrate threat intelligence – use insights from your AI platform and from the broader security community to stay ahead of new attack techniques.
- Invest in training – your security team should understand how the AI works, how to interpret its decisions, and when to override automated actions.
- Test and iterate – run regular tabletop exercises and red‑team scenarios that challenge your AI defense, especially against zero‑day exploits.
By following these steps, you can build a cyber defense that leverages the full potential of frontier AI – not just reacting to threats, but outpacing them at machine speed.